Jarvis OJ-从Reverse到去世
Jarvis OJ-从Reverse到去世
-
FindKey
pyc逆向
uncompyle得到.py
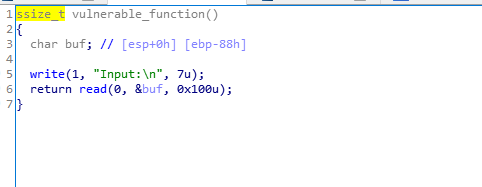
# uncompyle6 version 3.2.5 # Python bytecode 2.7 (62211) # Decompiled from: Python 2.7.15rc1 (default, Nov 12 2018, 14:31:15) # [GCC 7.3.0] # Embedded file name: findkey # Compiled at: 2016-04-30 17:54:18 import sys lookup = [ 196, 153, 149, 206, 17, 221, 10, 217, 167, 18, 36, 135, 103, 61, 111, 31, 92, 152, 21, 228, 105, 191, 173, 41, 2, 245, 23, 144, 1, 246, 89, 178, 182, 119, 38, 85, 48, 226, 165, 241, 166, 214, 71, 90, 151, 3, 109, 169, 150, 224, 69, 156, 158, 57, 181, 29, 200, 37, 51, 252, 227, 93, 65, 82, 66, 80, 170, 77, 49, 177, 81, 94, 202, 107, 25, 73, 148, 98, 129, 231, 212, 14, 84, 121, 174, 171, 64, 180, 233, 74, 140, 242, 75, 104, 253, 44, 39, 87, 86, 27, 68, 22, 55, 76, 35, 248, 96, 5, 56, 20, 161, 213, 238, 220, 72, 100, 247, 8, 63, 249, 145, 243, 155, 222, 122, 32, 43, 186, 0, 102, 216, 126, 15, 42, 115, 138, 240, 147, 229, 204, 117, 223, 141, 159, 131, 232, 124, 254, 60, 116, 46, 113, 79, 16, 128, 6, 251, 40, 205, 137, 199, 83, 54, 188, 19, 184, 201, 110, 255, 26, 91, 211, 132, 160, 168, 154, 185, 183, 244, 78, 33, 123, 28, 59, 12, 210, 218, 47, 163, 215, 209, 108, 235, 237, 118, 101, 24, 234, 106, 143, 88, 9, 136, 95, 30, 193, 176, 225, 198, 197, 194, 239, 134, 162, 192, 11, 70, 58, 187, 50, 67, 236, 230, 13, 99, 190, 208, 207, 7, 53, 219, 203, 62, 114, 127, 125, 164, 179, 175, 112, 172, 250, 133, 130, 52, 189, 97, 146, 34, 157, 120, 195, 45, 4, 142, 139] pwda = [ 188, 155, 11, 58, 251, 208, 204, 202, 150, 120, 206, 237, 114, 92, 126, 6, 42] pwdb = [53, 222, 230, 35, 67, 248, 226, 216, 17, 209, 32, 2, 181, 200, 171, 60, 108] flag = raw_input('Input your Key:').strip() if len(flag) != 17: print 'Wrong Key!!' sys.exit(1) flag = flag[::-1] for i in range(0, len(flag)): if ord(flag[i]) + pwda[i] & 255 != lookup[i + pwdb[i]]: print 'Wrong Key!!' sys.exit(1) print 'Congratulations!!' # okay decompiling findkey.pyclookup = [ 196, 153, 149, 206, 17, 221, 10, 217, 167, 18, 36, 135, 103, 61, 111, 31, 92, 152, 21, 228, 105, 191, 173, 41, 2, 245, 23, 144, 1, 246, 89, 178, 182, 119, 38, 85, 48, 226, 165, 241, 166, 214, 71, 90, 151, 3, 109, 169, 150, 224, 69, 156, 158, 57, 181, 29, 200, 37, 51, 252, 227, 93, 65, 82, 66, 80, 170, 77, 49, 177, 81, 94, 202, 107, 25, 73, 148, 98, 129, 231, 212, 14, 84, 121, 174, 171, 64, 180, 233, 74, 140, 242, 75, 104, 253, 44, 39, 87, 86, 27, 68, 22, 55, 76, 35, 248, 96, 5, 56, 20, 161, 213, 238, 220, 72, 100, 247, 8, 63, 249, 145, 243, 155, 222, 122, 32, 43, 186, 0, 102, 216, 126, 15, 42, 115, 138, 240, 147, 229, 204, 117, 223, 141, 159, 131, 232, 124, 254, 60, 116, 46, 113, 79, 16, 128, 6, 251, 40, 205, 137, 199, 83, 54, 188, 19, 184, 201, 110, 255, 26, 91, 211, 132, 160, 168, 154, 185, 183, 244, 78, 33, 123, 28, 59, 12, 210, 218, 47, 163, 215, 209, 108, 235, 237, 118, 101, 24, 234, 106, 143, 88, 9, 136, 95, 30, 193, 176, 225, 198, 197, 194, 239, 134, 162, 192, 11, 70, 58, 187, 50, 67, 236, 230, 13, 99, 190, 208, 207, 7, 53, 219, 203, 62, 114, 127, 125, 164, 179, 175, 112, 172, 250, 133, 130, 52, 189, 97, 146, 34, 157, 120, 195, 45, 4, 142, 139] pwda = [ 188, 155, 11, 58, 251, 208, 204, 202, 150, 120, 206, 237, 114, 92, 126, 6, 42] pwdb = [53, 222, 230, 35, 67, 248, 226, 216, 17, 209, 32, 2, 181, 200, 171, 60, 108] flag="" for i in range(0, 17): flag += chr(lookup[i + pwdb[i]]-pwda[i] & 255) flag = flag[::-1] print flagPCTF{PyC_Cr4ck3r} -
软件密码破解-1
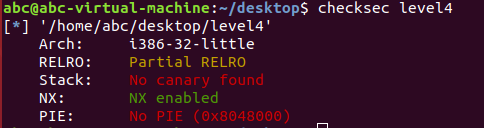
扔到IDA Pro里发现有一堆函数没法看
扔OD里
先查找一波看看有没有重要的字符串
定位到’‘你赢了’‘,往上翻可以看到一堆比较,应该是关键函数
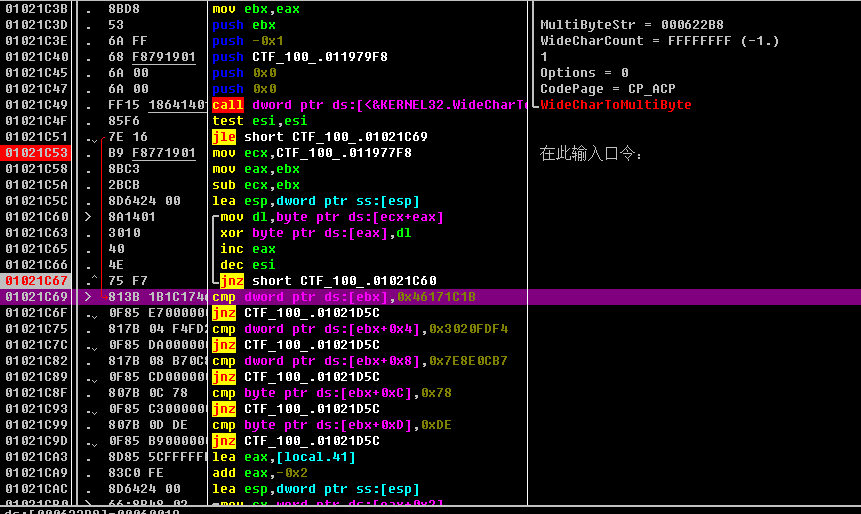
在01021C53断,数据窗口跟随CTF_100_.011977F8
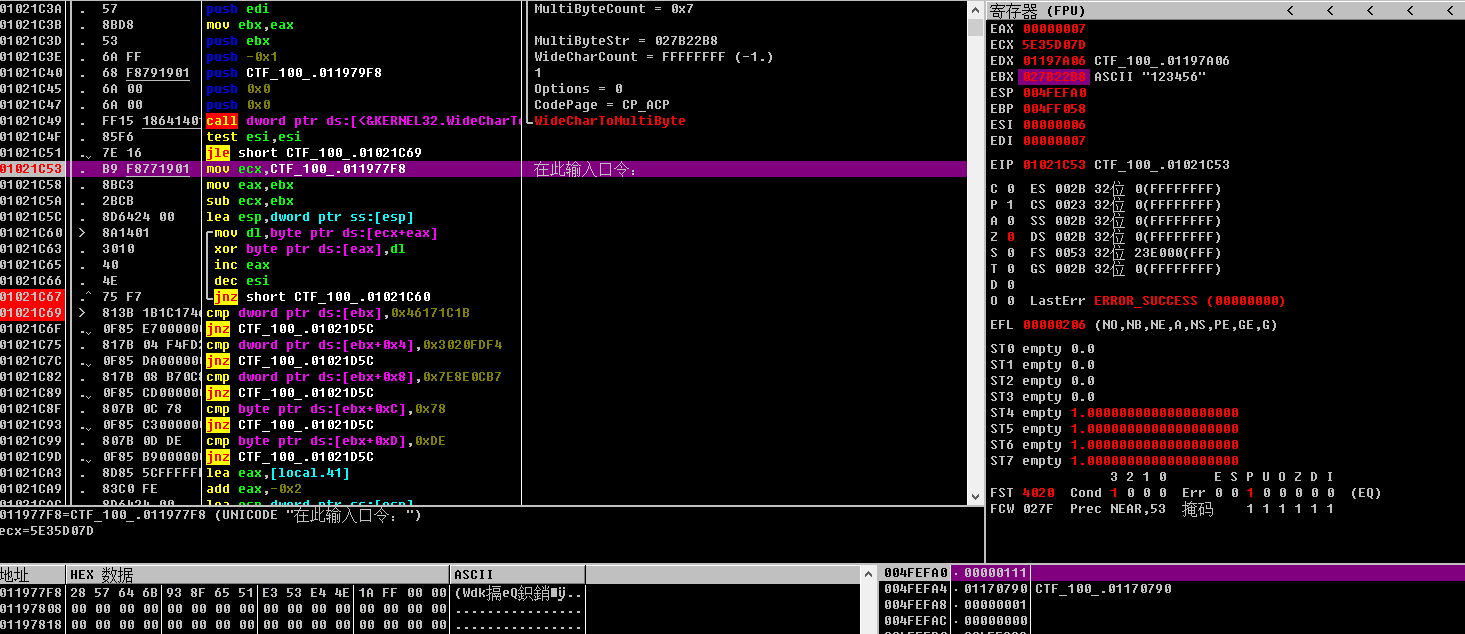
输入的数据在ebx,eax=ebx
ecx=CTF_100.011977F8-ebx=CTF_100_.011977F8-eax=dl=ecx+eax=CTF_100_.011977F8CTF_100_.011977F8是
x28, 0x57, 0x64, 0x6B, 0x93, 0x8F, 0x65, 0x51, 0xE3, 0x53, 0xE4, 0x4E, 0x1A, 0xFF每次循环将eax中取出一位和CTF_100_.011977F8中的一位异或,然后eax+1,eax可看作下标
循环结束后比较异或后每一位的值
异或后的值应为
0x1B, 0x1C, 0x17, 0x46, 0xF4, 0xFD, 0x20, 0x30, 0xB7, 0x0C, 0x8E, 0x7E, 0x78, 0xDEa = [0x28, 0x57, 0x64, 0x6B, 0x93, 0x8F, 0x65, 0x51, 0xE3, 0x53, 0xE4, 0x4E, 0x1A, 0xFF] b = [0x1B, 0x1C, 0x17, 0x46, 0xF4, 0xFD, 0x20, 0x30, 0xB7, 0x0C, 0x8E, 0x7E, 0x78, 0xDE] flag = "" for i,j in zip(a,b): flag += chr(i ^ j) print flagflag{3Ks-grEaT_j0b!} -
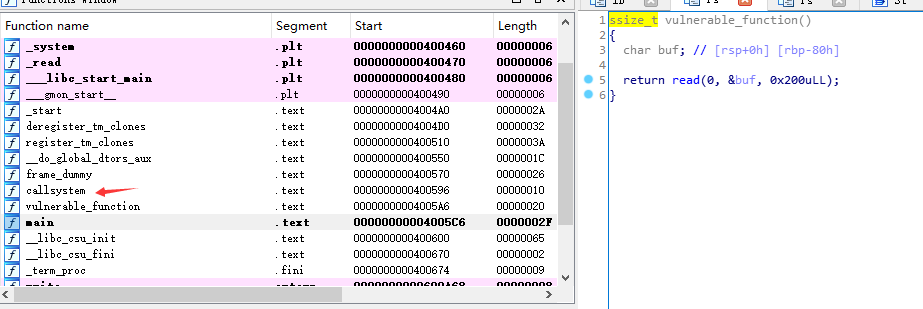
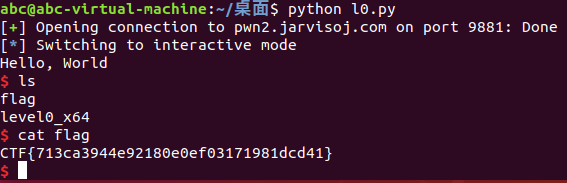
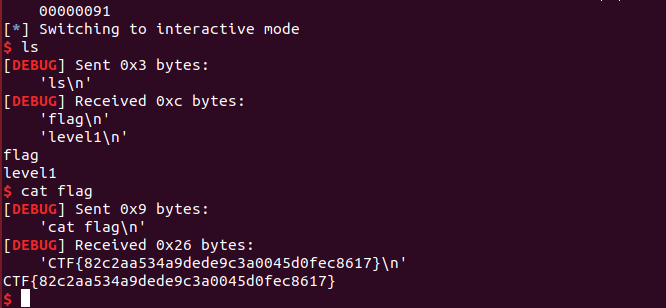
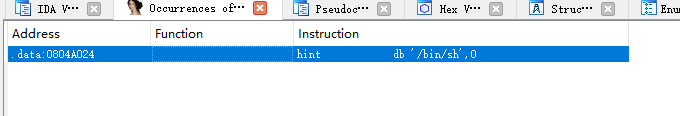
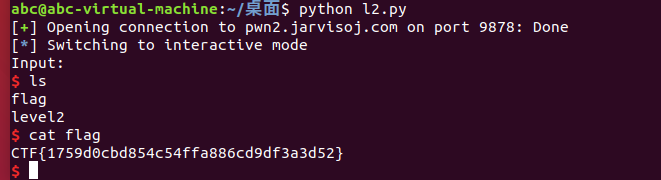
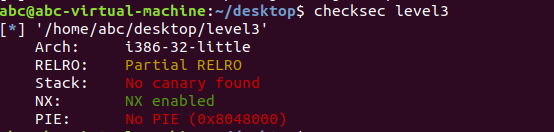
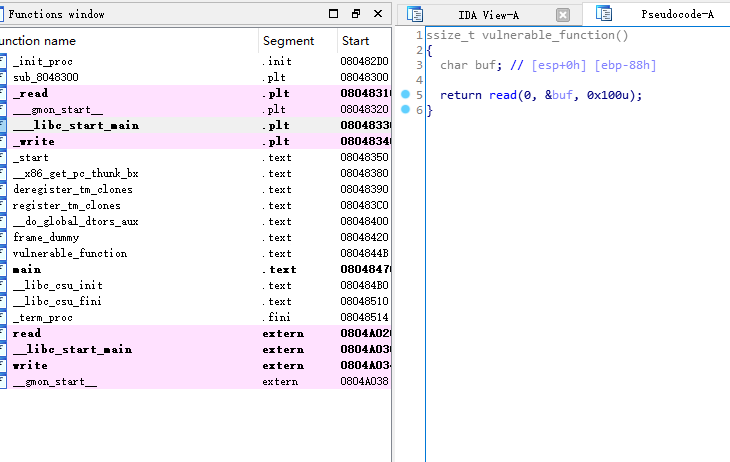
[61dctf]stheasy
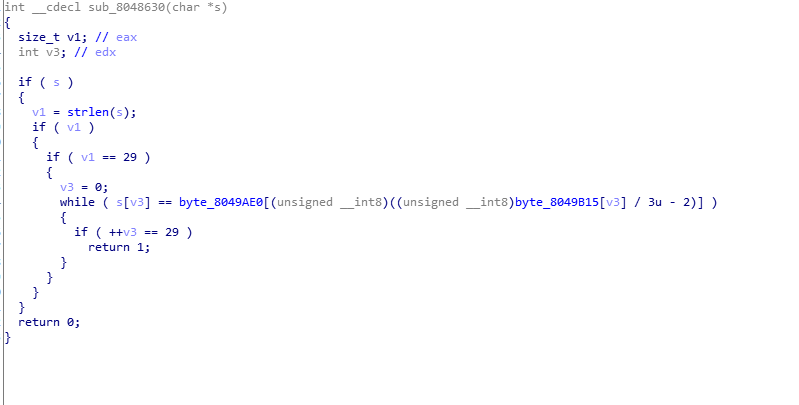
看一下8049AE0和8049B15
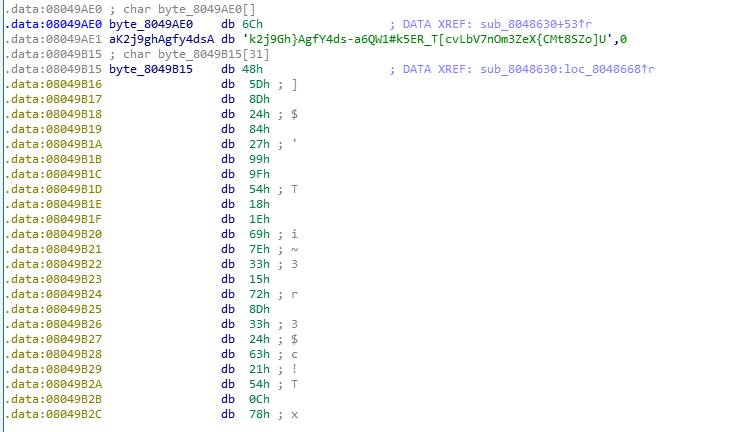
直接写脚本
a = "lk2j9Gh}AgfY4ds-a6QW1#k5ER_T[cvLbV7nOm3ZeX{CMt8SZo]U" b = [0x48,0x5D,0x8D,0x24,0x84,0x27,0x99,0x9F,0x54,0x18,0x1E,0x69,0x7E,0x33,0x15,0x72,0x8D,0x33,0x24,0x63,0x21,0x54,0x0C,0x78,0x78,0x78,0x78,0x78,0x1b] flag = "" for i in b: flag += a[i/3 - 2] print flagkctf{YoU_hAVe-GOt-fLg_233333} -
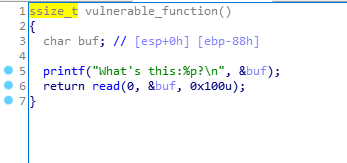
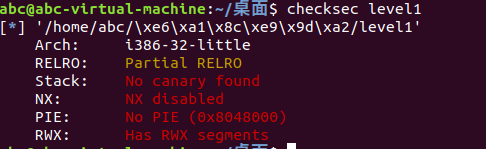
DD - Hello
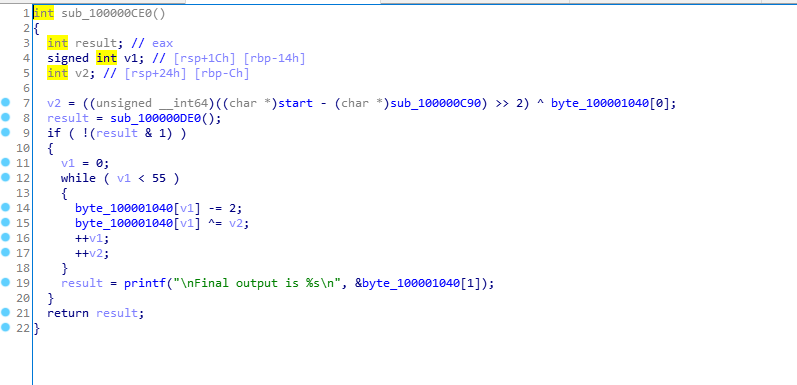
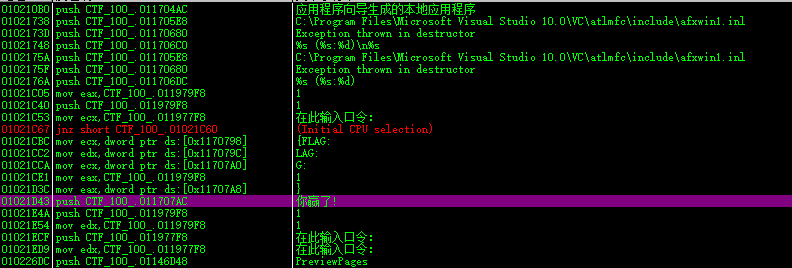
其他函数都没啥用,俺寻思这是关键函数
v2根据strat和sub_100000C90的地址计算
a = [0x41,0x10,0x11,0x11,0x1B,0x0A,0x64,0x67,0x6A,0x68,0x62,0x68,0x6E,0x67,0x68,0x6B,0x62,0x3D,0x65,0x6A,0x6A,0x3D,0x68,0x4,0x5,0x8,0x3,0x2,0x2,0x55,0x8,0x5D,0x61,0x55,0x0A,0x5F,0x0D,0x5D,0x61,0x32,0x17,0x1D,0x19,0x1F,0x18,0x20,0x4,0x2,0x12,0x16,0x1E,0x54,0x20,0x13,0x14] v2 = (0x100000CB0-0x100000C90>>2)^a[0] flag = "" for i in range(55): flag += chr((a[i]-2) ^ v2) v2 += 1 print flagDDCTF-5943293119a845e9bbdbde5a369c1f50@didichuxing.com